Skill Development Initiatives
Beyond Courses — Building Investigation Capability
SDI programs extend beyond structured training to equip participants with investigation tools, operational environments, and continuous learning frameworks. Designed for individuals and institutions building long-term forensic capability.
🔧
Forensic Tool Development
Participants engage in the development cycle of CRIMATON's forensic tools — contributing to real instrument development while deepening their technical understanding of how investigation software is built and validated.
📊
Investigation-Focused Software Projects
Structured project work in which participants design, build, and test purpose-built investigation modules. Projects are evaluated against forensic integrity standards and contribute to the CRIMATON tooling ecosystem.
🌐
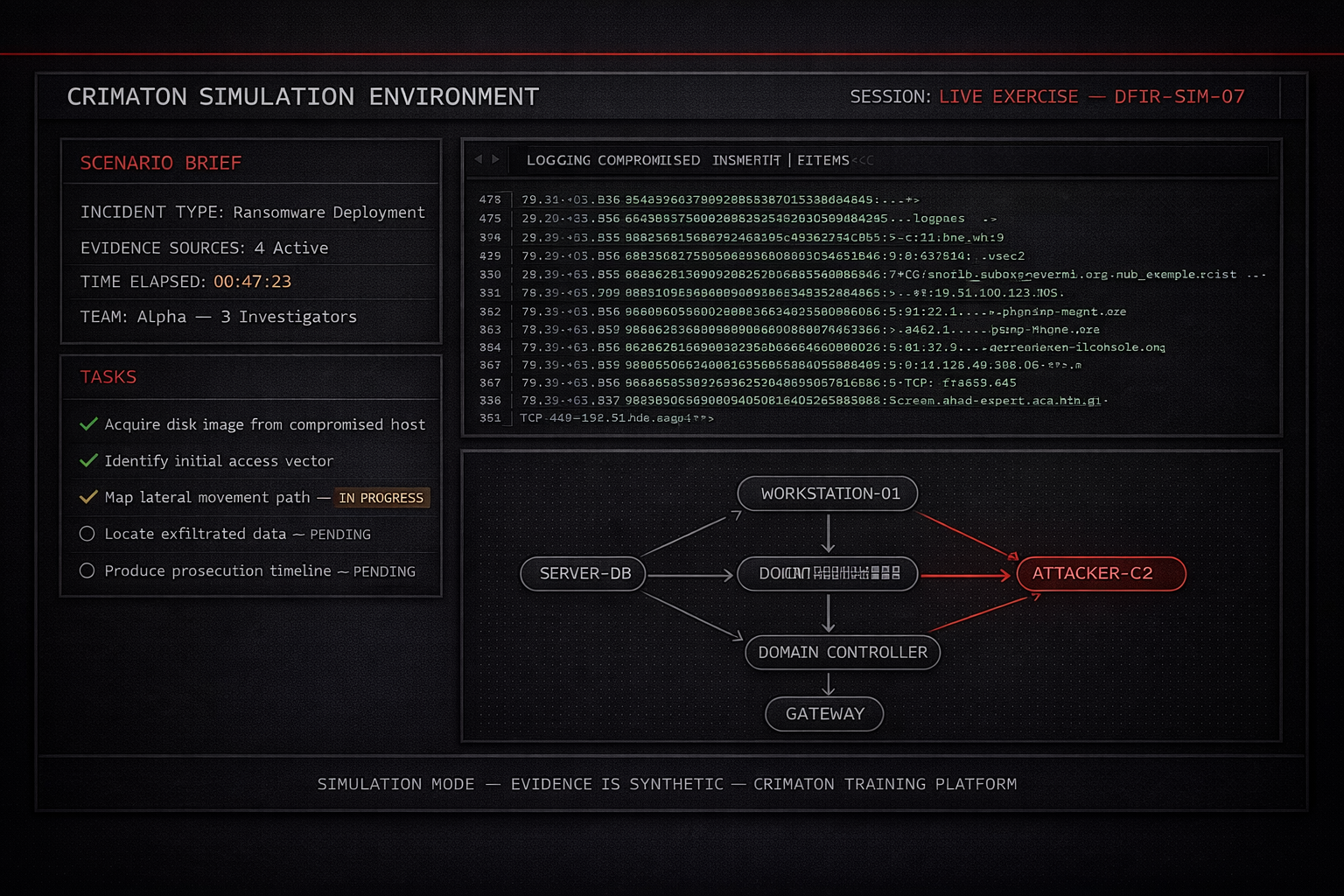
Simulation Environments
Access to CRIMATON's controlled investigation simulation environments for ongoing practice outside of formal training programs. Scenarios are updated to reflect current threat actor TTPs and emerging cybercrime patterns.
📚
Case-Based Learning Systems
Structured case libraries constructed from real investigation archetypes. Participants work through case resolution from initial evidence intake through prosecution referral — developing procedural fluency and investigative judgment.
🏆
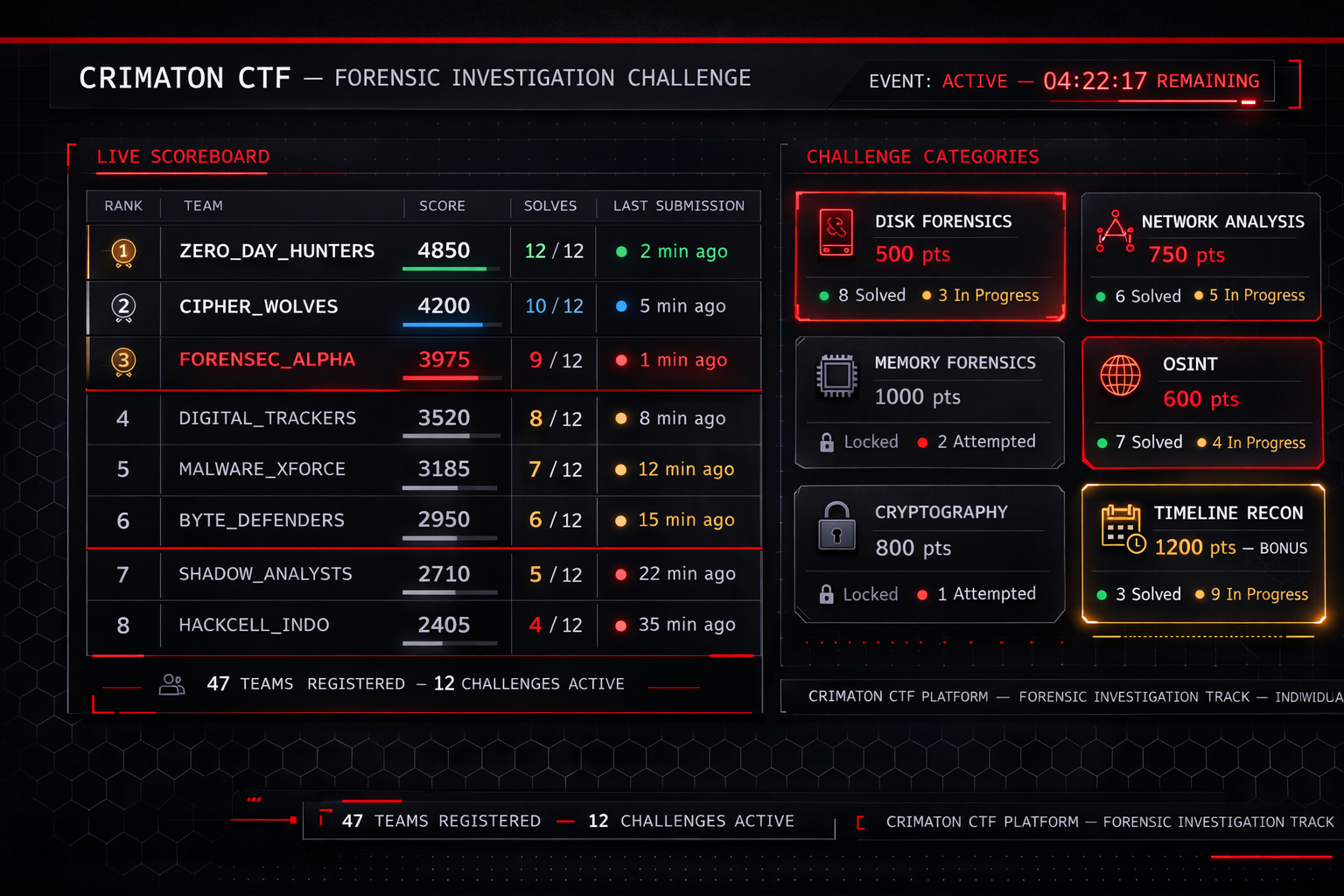
CTF Competition Program
Organised Capture the Flag competitions structured around forensic investigation categories — disk forensics, network analysis, memory examination, and OSINT challenges. Individual and team formats available for ongoing skill assessment.
👥
Career Mentorship & Placement
Mentorship from active digital forensics practitioners for SDI participants pursuing careers in law enforcement, enterprise security, or forensic consulting. Structured guidance on case-building, portfolio development, and professional readiness.