Investigation-Grade Software
CRIMATON Solutions
Purpose-built software for digital forensic investigators, incident response teams, and cybercrime units. Every platform is designed around the operational reality of investigations — not theoretical use cases.
Each CRIMATON solution addresses a specific phase of the investigation lifecycle — from initial evidence acquisition through to prosecution-ready reporting. Built by practitioners. Validated in the field.
Digital evidence acquisition and analysis — chain-of-custody preserved
Solution 01
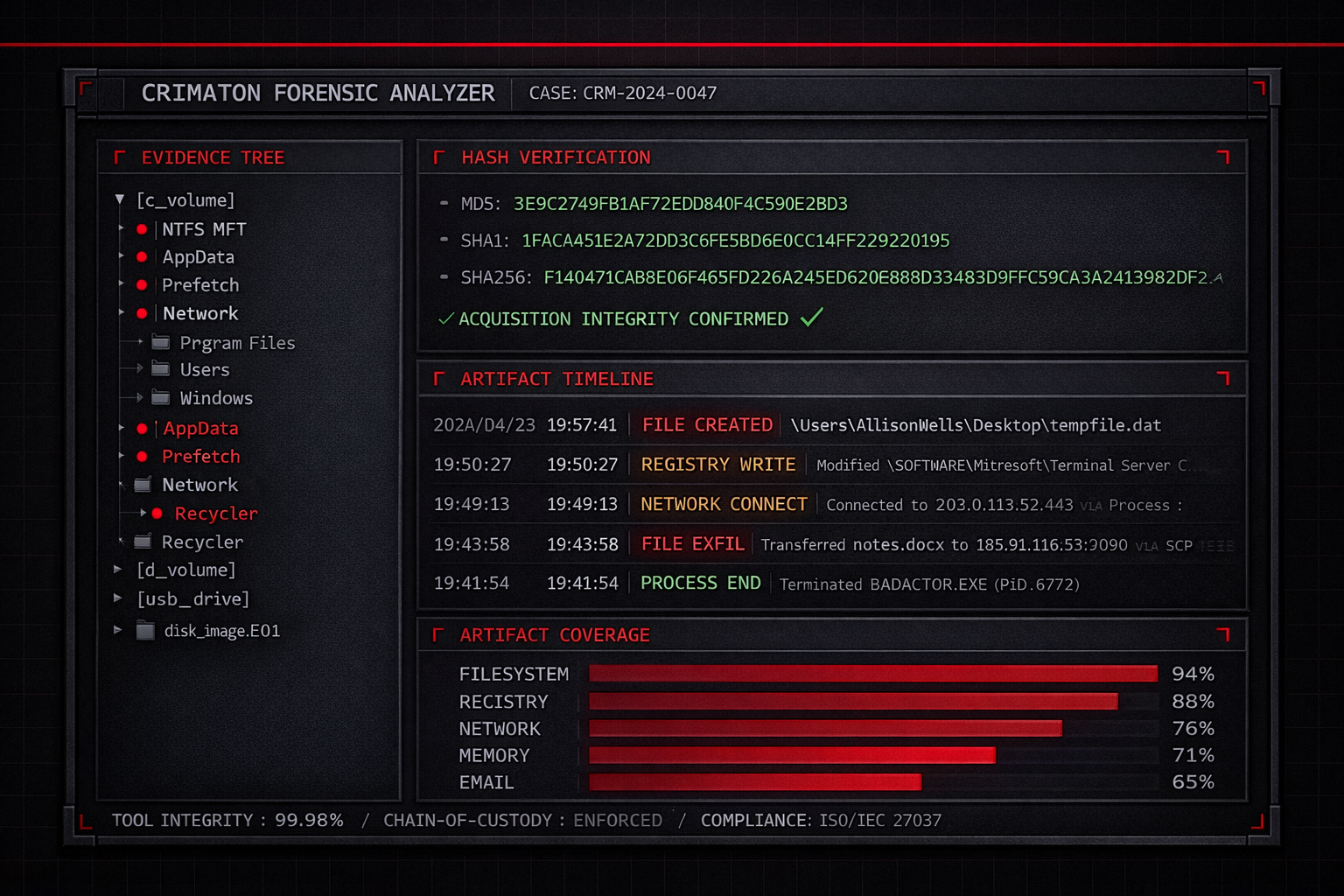
Digital Forensics & Evidence Analysis Software
The Problem
- Evidence mishandled without write-blocked acquisition is inadmissible in court
- Manual hash verification is error-prone and breaks chain-of-custody
- Fragmented artifact sources make timeline reconstruction slow and incomplete
CRIMATON's Approach
- Write-blocked acquisition across disk, mobile, and cloud environments
- Automated MD5 & SHA-256 hash verification at every stage
- Artifact correlation across file systems, registry, browser, and communication logs
Operational Impact
- Defensible, court-ready evidence trail from acquisition to final report
- Every analyst action logged with credentials, timestamps, and hash validation
- Output structured for expert witness testimony and legal proceedings
Capabilities

Breach containment and forensic triage for enterprise environments
Solution 02
Incident Response & Breach Investigation Software
The Problem
- Active breaches demand simultaneous containment, evidence preservation, and reporting
- Unstructured responses destroy forensic value and allow re-entry
- No standardised playbooks means every team improvises under pressure
CRIMATON's Approach
- Structured playbooks for ransomware, exfiltration, insider threat, and supply chain incidents
- Simultaneous volatile memory, process, network, and auth log collection during triage
- Systematic root cause and attack vector documentation throughout response
Investigative Value
- Full attacker TTP and lateral movement documentation in MITRE ATT&CK format
- Findings directly feed remediation actions and regulatory breach notifications
- Incident timelines exportable for legal, compliance, and insurance use
Capabilities
Open-source intelligence collection and actor attribution workflows
Solution 03
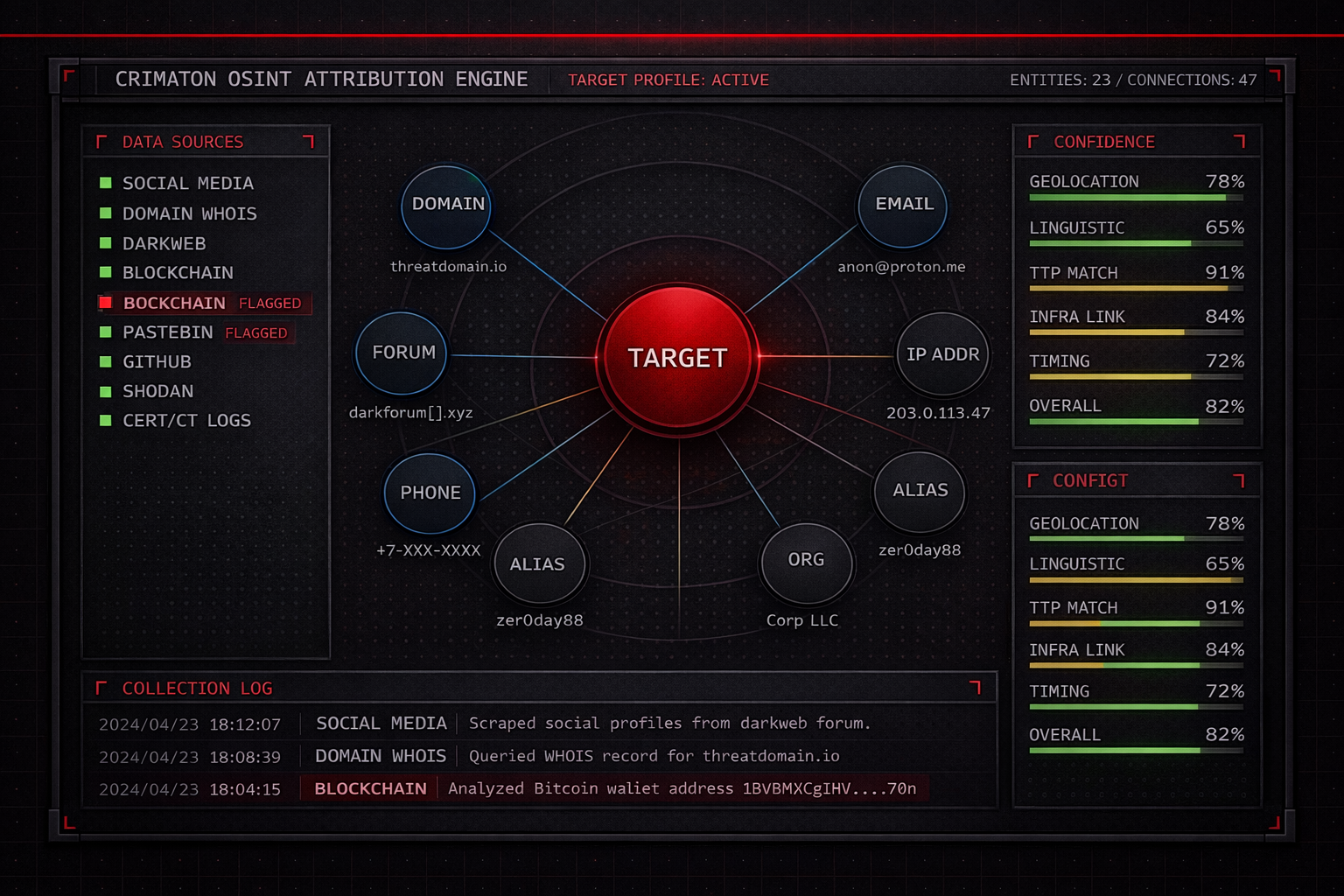
OSINT & Threat Attribution Software
The Problem
- Actor attribution requires collection across social platforms, domains, blockchain, and dark web
- Manual collection is slow, incomplete, and legally fragile without provenance records
- Unstructured OSINT rarely survives legal scrutiny or cross-agency sharing
CRIMATON's Approach
- Structured collection workflows per target — individuals, domains, IPs, wallets
- Every data point timestamped, source-tagged, and archived for evidentiary use
- Link analysis and entity relationship mapping surface connections across datasets
Investigative Value
- Attribution packages structured for law enforcement referrals and prosecutorial briefs
- Collection methodology documented to meet legal scrutiny across jurisdictions
- Intelligence sharing-ready output compatible with partner agency formats
Capabilities

Cybercrime analysis from initial complaint through prosecution referral
Solution 04
Cybercrime & Fraud Investigation Software
The Problem
- Fraud and cybercrime cases draw evidence from email headers, financials, devices, and platforms simultaneously
- Without structured workflows, investigations stall at evidence assembly
- Most cases never reach actionable prosecution due to documentation gaps
CRIMATON's Approach
- End-to-end case management from complaint intake through prosecution referral
- Financial tracing maps fund flows across banking systems and cryptocurrency networks
- Communication analysis reconstructs criminal coordination across platforms
Operational Impact
- Structured case dossiers that meet law enforcement evidentiary standards
- Unified case timeline normalised from all heterogeneous evidence sources
- Full audit trail maintained across investigators, prosecutors, and victim support
Capabilities
Custom Forensic Solutions for Agencies and Defence Organisations
Standardised software products are rarely designed with law enforcement operational constraints in mind. CRIMATON develops custom investigation platforms, forensic tool integrations, and analysis systems tailored to the specific evidentiary requirements, classification environments, and operational protocols of government bodies, police units, and defence agencies.
Our engagements are conducted under appropriate confidentiality agreements and designed for deployment in air-gapped and classified environments where required. We work directly with your technical and legal teams to ensure every component meets applicable standards — including those specific to your jurisdiction's court admissibility requirements.
Need something specific for your organisation? Contact us now — initial consultations are confidential.
Direct Contact
Jalandhar, Punjab, India
Tools Are Only Part of the Equation.
Effective forensic investigation requires trained operators. Our DFIR Training & Skill Development programs are designed to close the gap between the capabilities of your tools and the skills of your team.